At a glance
$2M-$5M
2021 - 2022
1 to 2 years
Ongoing
Drupal, LAGOON
Federal government
Design & user research, Build & migration
GovTech, Whole of government, Web development
User needs, Agile delivery, Security, Design
Overview
The challenge
A federal agency (that can’t be named for security reasons) was running its online portal on an old version of MS SharePoint. The portal had a high cost of ownership, many functional gaps, was slow to respond, and was visually unappealing to the user. It was no longer fit for purpose.
The transformation
Salsa Digital, along with our partners and Oliver , designed and built a new central portal. The new portal has better support for user journeys, improved functionality, improved performance and is highly secure. It’s also providing far more options to agency content authors to enhance their content visually and making it easier for them to publish data.
The outcomes
- A new, user-focused portal with improved visual design
- An improved content editing experience
- Migration of 140K+ content items onto the new portal with all relevant metadata
- Improved portal security, performance and usability
Full case study
Below is more detail on this project, including details of the security design, visual design and site build.
The challenge — a costly, outdated portal
The client had an outdated portal with a range of technical, operational and usability issues. The portal was built on Microsoft SharePoint and had become expensive and difficult to maintain.
Stakeholder feedback pointed to significant problems affecting the portal and its users. Users had disengaged from the portal due to broken functionality, ageing visual design, inadequate operational support, and usability/user experience issues.
The transformation — a secure, flexible, engaging portal with lower cost of ownership
The agency’s transformation focused on:
- A user-centric design (UCD) process for visual design
- Architecting the portal for security
The UCD is based on Digital Transformation Agency (DTA) best service delivery. This ensures representative users are included in the design process to validate the user experience prior to build. Salsa’s creative partner Oliver Grace led the design process to ensure the final portal was visually appealing and user-centric.
The portal needed to launch at ISM OFFICIAL: Sensitive. Salsa drew on our experience securing whole-of-government digital platforms such as GovCMS and Victoria’s Single Digital Presence to launch the portal with the required security.
Project delivery blueprint
The project was, and continues to be, a significant program of work. A rigorous transition-in and service delivery plan was required. Salsa designed a delivery model to meet the federal agency’s needs.
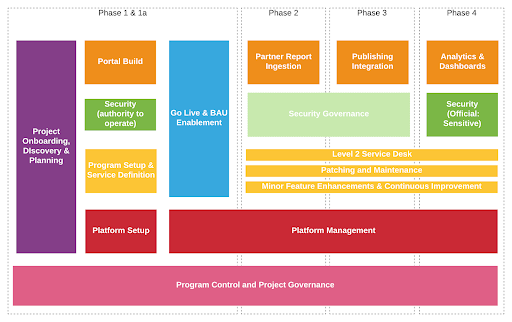
The project was broken into four key phases:
Phase 1 — A new portal with interim capability, migration of 140K content pieces and phase 1a enhancement sprints (complete)
Phase 2 — Migration of existing 1.2TB of data and build of new report system (in progress)
Phase 3 — End-to-end integration with the existing publishing system (upcoming)
Phase 4 — Creation of business intelligence reports (upcoming) and ISM PROTECTED (descoped)
Each phase is being delivered as discrete agile projects, with their own discovery, planning, build, UAT and go-live.
A series of service streams addressed critical aspects of the project, namely:
Portal build (orange) — Delivering the technical solution across each phase
Security and accreditation (green) — Delivering phase 1 to OFFICIAL: Sensitive
Program services (yellow) — Establishing tools and processes, and support for the program post phase 1 launch
Platform management (red) — Establishing the secure, dedicated infrastructure
Program control and governance (pink) — Coordinating activities across the streams during each phase
Security design
The federal agency portal manages sensitive data shared with authorised government agencies and partners. Given this, it was imperative that the new portal was appropriately secured. The Australian Government Information Security Manual (ISM) is a framework used to apply risk-based management to protect systems and data from cyber threats. The launch pathway was starting with ISM OFFICIAL: Sensitive.
Salsa’s security design included:
Using a dedicated cluster to host the portal for the highest level of isolation from cyber threats.
Ensuring production data is only used in relevant environments (production and staging) with all other environments using sanitised data.
Using processes and systems from Salsa’s GovCMS experience where appropriate — Salsa had previously led the accreditation of GovCMS to ISM OFFICIAL: Sensitive (see GovCMS security case study). This knowledge and experience was used as a baseline for this project.
Designing for security at every level — The Drupal application is architected for security requirements as are all the processes, people and technology involved.
Using the following services via amazee.io:
Fully managed content delivery network (CDN)
Fully managed next-gen web application firewall (WAF) (formerly Signal Sciences)
Origin shield
The service enables origin to only accept traffic from the CDN or a pre-approved IP list, which has passed high level WAF rules.
Salsa worked with the client to perform an IRAP assessment. More details are in our dedicated security case study.
UCD process
The team at Oliver Grace (OG) followed a user-centric design process to design the portal with users in mind. Interviews with representative users and testing user journeys on early prototypes allowed validation of assumptions and iteration of the design. Salsa, OG and the client built confidence in the user experience prior to investing in the build (per DTA best practice service ).
Functional discovery
Salsa worked closely with our client to structurally review each area of the project scope. We then re-iterated functional JIRA stories for approval by the product owner. Areas of discovery included:
Desired report functionalities, e.g. the ability to create a PDF from the data, the ability to display related data, the ability to click on data tags that would take the user to the search page with the relevant topic filter set, the need for automatic ID generation, etc.
Desired landing page features, e.g. the ability to set automated filtered listings, the ability to promote content, the ability to add manual references to other portal pages, etc.
Desired workflow for content editors so content authors can review and approve each other’s work for publishing.
Subscriptions, so users can subscribe to specific data and receive the relevant alerts.
Editorial improvements, e.g. the ability for content authors to select data published on the day and automatically generate a compilation of this data automatically grouped based on a primary tag set.
The ability for the end user to provide feedback on the data, which is then relayed back to the individual authors.
Integrating the portal with another system, which would need to ingest data published in the new portal.
Generating draft data from an external source via a text file that’s generated from an external system.
Desired search requirements for editors and users.
Migrating 140K+ data assets from the predecessor with varying data models and validating this migration.
Desired login model for the portal.
Content data model
One of the early challenges of the project was to build a content data model. We needed to understand exactly how all the associated metadata correlates. This allowed us to build confidence that the system’s foundation was solid and we’d be able to support all the use-cases — for the frontend users, the content authors and the site administrator. We approached this with great attention to detail as we knew that if the setup wasn’t right we could easily be blocked. Only once this data model was reviewed and approved by relevant stakeholders did we move on to building the solution.
Development
Salsa used agile methodology to deliver the project incrementally, demoing the status quo every two weeks and allowing the client to do user acceptance testing (UAT) incrementally as well. This allowed Salsa to flexibly react to changing requirements and to learn more about the user and editorial needs throughout the project. Larger changes in scope were managed together with the client, allowing us to share the risk and progress.
Training/stakeholder testing
As we were reaching the end of phase 1, we started to draft the training materials for the various roles — member, content author and site administrator. This also put us in a great position to deliver preliminary training to a pool of content authors, which meant they could properly test the system prior to launch with enough time for us to make minor amendments. A final training session and in-depth documentation was then delivered closer to the go-live date.
Next steps
Now that the portal has launched and is being used every day, opportunities for small optimisations appear. We’re working with client stakeholders to collate feedback and have set up another workshop to discuss desired changes with Oliver Grace and brainstorm solutions. Once our federal agency client has signed off any relevant design amendments we’ll create JIRA tickets for the changes and prioritise them along with other functional changes.
We’ve now also launched into discovery for phase 2 and 3 (making sure that we understand how each of these phases will impact each other).
We have, of course, also officially entered business as usual (BAU) mode, which means that we’re handling support requests, updating modules on a monthly basis and applying security patches as they become available.
The outcomes — a secure, more engaging portal
A new, user-focused portal with improved visual design
An advanced experience for content editors
Greater control on landing pages and the ability to promote content
Improved portal security, performance and usability
Migration of 140K + data assets, onto the new portal with relevant metadata
Better search functionality
No licensing fees and a lower cost of ownership
An effective support model for portal support and maintenance
